Had Your Service Person Change My Default to 5 Minutes in of Arts
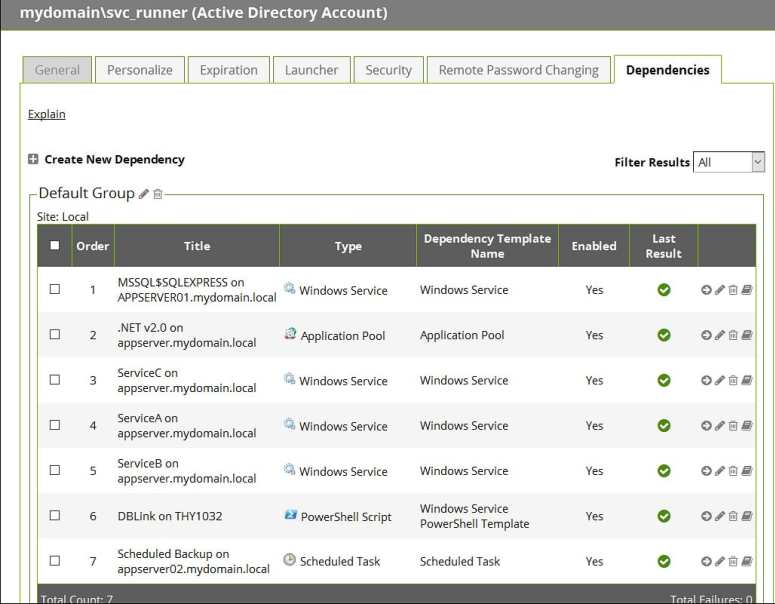
Service accounts don't have to be a nightmare. Arrive command now. Service accounts are typically used in operating systems to execute applications or run programs, either in the context of organisation accounts (loftier privileged accounts without any password) or a specific user account, usually created manually or during software installation. On Unix and Linux they are often known as init or inetd, and can as well launch programs. Can anyone think who installed this application? And what was the service account password? All too ofttimes asked questions! Service business relationship management is a task that'southward all too often overlooked as the accounts can be a pain for organizations to control. Especially across multiple accounts for different services, tasks, and other applications, and in sync—it's fourth dimension-consuming and error-prone when done manually. Service account password direction is another challenge: administrators tin can't safely change a service account password if they don't know where it's used without the risk of bringing downwardly other applications. Download our free eBook: Service Business relationship Security For Dummies Frequently, in software installations, the countersign for the service accounts either remains the default vendor password (easily found on the cyberspace) or is in the memory of the consultant who installed the software. As a result of these bad practices, service account and application passwords are often set to never expire and subsequently remain unchanged year later on year. Failing to change service account passwords represents a meaning security risk because service accounts often have admission to sensitive data and systems. There is no shortage of these risky accounts. Near organizations have more service accounts than employees, sometimes upwards to v times as many! The accounts are oft provisioned without any automated controls set in place. If they are provisioned without any robust process in identify then that begs the question: is anyone keeping runway of these service accounts when they are no longer needed? This is, unfortunately, common in many organizations, and when it comes to securing the organization against cyber-attacks, it's a really bad do. I accept seen then many incidents in which the It Operations team are running effectually trying to figure out the service account password during a failed upgrade, patch deployment, maintenance mishap, or fifty-fifty worse—during a major security incident. At this point, it is already too late, with finish-users and the executive team screaming for answers. Because service accounts are often managed manually from cradle to grave, they are prone to errors. HERE'S AN Example: A Loftier-POWERED SPREADSHEET EXPERIENCE I was in one case hired past a country-of-the-art power station. Information technology was relatively new, fully automated with remote controls, and they wanted me to review its cybersecurity protection and security control. The physical security was impressive. The security organization could tell when visitors were five minutes away, gave security avant-garde warning for when visitors should make it, what they would be driving, and how many people were in the vehicle. If visitors arrived 1 minute before or after the prediction, they would have to bargain with armed guards. All physical doors had access controls, including the engine rooms. Once inside the engine rooms, each engine had its own control valves to physically change pressure level and water flow. The control valves were not secured, although the chance of tampering was low. Command and command via the programmable logic controllers (PLCs) and SCADA command systems all featured the latest and greatest cybersecurity advanced threat protection, with millions spent to prevent cybersecurity attacks. They had built themselves a physical and cyber fortress. And so it happened. Sitting on the tabular array next to the controls was a printed page. It contained all the IP addresses, usernames, and passwords for each command station and the service accounts. They had non been changed in more than four years and had all been installed past the manufacturer with default vendor credentials. Anyone could have made copies of this listing: visitors, onetime employees, or fifty-fifty contractors. Anyone could have taken a smartphone picture and and so instigated an assault at their leisure. The ability station never would accept seen it coming. A Privileged Service Business relationship with default vendor password can be the difference between a unproblematic perimeter alienation and a cyber ending Practise not be another statistic. Get in control of managing your service accounts now. Prioritizing this will non but assistance salve you time and money; it will also improve your cybersecurity and reduce your take a chance of a cyber-attack. Use the Privileged Access Management Lifecycle to get control of your Service Accounts Like any IT security measure designed to aid protect critical information assets, managing and protecting service account requires both a programme and an ongoing program. You must place which service accounts should be a priority in your system. Ascertain Define and classify service accounts . Every organization is different, so you lot need to map out what important applications and programs rely on data, systems, and access. One approach is to reuse a disaster recovery plan that typically classifies of import applications and specifies which need to exist recovered get-go. Make sure to align your service accounts to your business concern risk and operations. Discover Observe your service accounts. Apply automated PAM software to identify your service accounts, and implement continuous discovery to curb service account sprawl. This helps ensure full, ongoing visibility of your service account landscape crucial to combating cybersecurity thursdayreats. Try our free Privileged Account Discovery Tools for Windows. Manage and protect Protect your service account passwords. Proactively manage, monitor, and control service business relationship admission with countersign protection software. Your solution should automatically notice and store service accounts; schedule password rotation; audit, analyze, and manage activeness; and monitor password accounts to quickly discover and respond to malicious activity. Monitor Monitor service business relationship activeness. Your PAM solution should exist able to monitor and record service account activity. This will assist enforce proper behavior and avoid mistakes by employees and other It users because they know their activities are being monitored. Find aberrant usage Track and alert on service account behavior. With upwards to 80% of breaches involving a compromised user or privileged account, gaining insights into service account access is a meridian priority. Ensuring visibility into the admission and activity of your service accounts in existent-time will help spot suspected business relationship compromise and potential corruption. For instance, monitoring when a service account has been used to log on to a system. Respond to incidents Prepare an incident response plan in case a service account is compromised. When a service account is breached, simply changing service account passwords or disabling the service business relationship is non acceptable. If compromised by an outside attacker, cyber criminals tin install malware and even create their ain service accounts or other privileged accounts. Review and audit Audit and analyze service account activity . Continuously observing how service accounts are being used through audits and reports will assist identify unusual behaviors that may signal a breach or misuse. These automatic reports also assistance runway the cause of security incidents, as well equally demonstrate compliance with policies and regulations. Make up one's mind if service accounts are still required, review security controls, and update expiration dates. With a robust Privileged Access Direction solution you can really get in control of your service accounts What does service account security like this cost? Not as much as you recollect. Go a free quote for your organization. 

How to get started with an constructive Service Account Management programme

Source: https://delinea.com/blog/service-account-management-101-cta-b
0 Response to "Had Your Service Person Change My Default to 5 Minutes in of Arts"
Post a Comment